The 5-minute cybersecurity audit every fintech should run
For many fintech and crypto companies, a cybersecurity audit is still seen as a compliance formality — quarterly at best, or only after an incident. But threats don’t wait for scheduled audits. Attackers move quickly, and even minor oversights can lead to breaches, fines, and reputational loss.
A simple 5-minute cybersecurity audit won’t replace full testing, but done regularly, it can catch critical red flags before they escalate, save you millions in fines and reputational loss — and it will help keep your business aligned with regulatory expectations. Most modern frameworks around the globe expect companies to demonstrate ongoing cybersecurity governance, not just point-in-time compliance.

Why a simple and regular cybersecurity audit matters
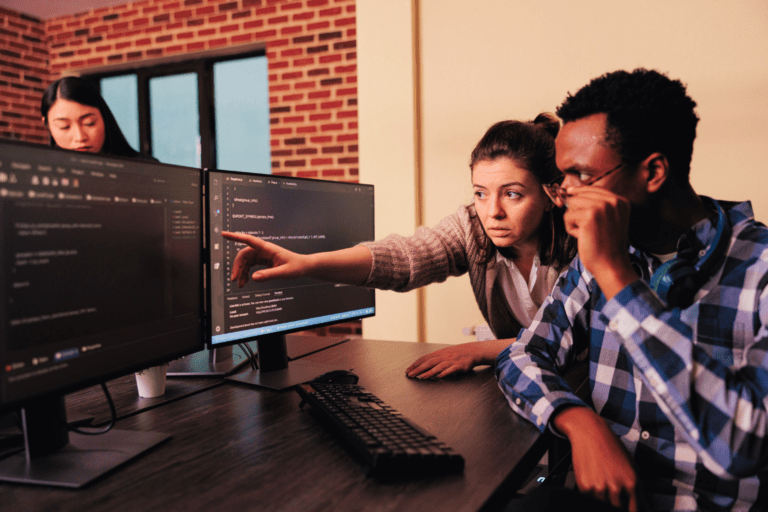
Cyberattacks don’t necessarily start with sophisticated exploits — they are more likely to start with overlooked basics: forgotten admin accounts, missed patches, misconfigured permissions. In fact, according to Verizon’s 2025 Data Breach Investigations Report, more than 60% of breaches involved vulnerabilities that could have been mitigated through basic security hygiene such as a routine internal cybersecurity audit. These gaps often slip through during slower business cycles — like summer or holiday periods — when security teams are thinly staffed and attackers know companies are less vigilant.
The impact of catching those issues in time is measurable. Organizations that proactively deployed security automation — including incident response readiness and regular assessments — reduced breach costs by an average of $1.9 million. Faster detection means faster containment and lower fallout across compliance, operations, and customer trust.
In the EU, GDPR violations can cost up to €20 million; in the UAE, cybersecurity laws impose strict compliance on financial entities; and in the U.S., agencies like the SEC demand rapid disclosure of incidents. A regular cybersecurity audit helps businesses meet these rising regulatory expectations.
So how do you turn this into a habit? It can start with just five minutes. Here’s a simple step-by-step guide your team can follow — weekly or bi-weekly — to stay ahead of the basics.
The 5-minute cybersecurity audit: step-by-step
A 5-minute cybersecurity audit is not a substitute for a full penetration test, a risk-based vulnerability assessment, or a formal Incident Response Plan (IRP). Those require in-depth tools, expert analysis, and coordinated protocols.
But a lightweight check like this can still surface the kinds of gaps attackers routinely exploit — and catching them early is often what prevents a breach. In fintech and crypto environments, where speed and integrations dominate, these signals are especially valuable.
Here’s what to check in just a few minutes:
1. Review user access and privileges
Dormant or excessive accounts — especially with admin rights — are one of the most common entry points.
- Are all user and administrator accounts still active and necessary?
- Have any former employees or vendors retained access?
- Is MFA enforced on all privileged accounts?
If gaps exist: Disable unused accounts, enforce MFA everywhere, and update role-based access controls.
2. Check for pending updates and patching gaps
Attackers weaponize known vulnerabilities within days.
- Are core systems, apps, and APIs fully updated?
- Are any high-severity CVEs left unpatched?
If gaps exist: Prioritize patching internet-facing systems and automate vulnerability scanning where possible.
3. Scan for unsecured endpoints and devices
Unmonitored endpoints, from laptops to mobile wallets, create unmanaged risk.
- Are all devices covered by EDR/antivirus?
- Has anything unfamiliar connected to your network recently?
If gaps exist: Ensure all devices are enrolled in your security stack, block rogue devices, and enforce BYOD policies.
4. Review access logs for suspicious activity
Unauthorized access often shows up first in your logs.
- Any failed login attempts from foreign IPs?
- Off-hours access without reason?
- Disabled accounts being used?
If gaps exist: Investigate through your SIEM or cloud console, and escalate suspicious activity for analysis.
5. Validate backup and encryption practices
Recovery depends on reliable, secure backups.
- Are backups recent, tested, and segregated from production?
- Is sensitive data encrypted in transit and at rest?
If gaps exist: Test backup recovery now, implement strong encryption, and move backups to secure, immutable storage.
What to do when you find something bigger
Sometimes the check-up surfaces issues that go beyond “quick fixes” — like repeated unauthorized login attempts, outdated third-party integrations, or anomalies in transaction logs. These are problems that need deeper investigation.
The key steps are:
- Don’t panic — but don’t ignore it either.
- Contain what you can by disabling accounts, isolating endpoints, or cutting off suspicious integrations.
- Document everything (logs, screenshots, timestamps) before making changes.
- Escalate internally — notify your IT or security lead immediately.
- Bring in an external expert for a full cybersecurity audit. Quick checks catch symptoms, but only a deeper assessment will uncover the full extent of your exposure.
In fintech and crypto, the risks are rarely linear. A single weak endpoint or exposed API can connect to broader vulnerabilities across liquidity flows, payment processors, or blockchain integrations. When surface checks raise concerns, the next step is a full review from specialists who understand the complexity of your ecosystem.
Go beyond a 5-minute cybersecurity audit with Clovr Labs
A quick cybersecurity audit is an excellent practice that can help spot vulnerabilities — but protecting a fintech or crypto business demands much more than hygiene checks.
That’s why at Clovr Labs we combine 360º attack exposure assessments, which map every possible entry point (including partners and integrations beyond your core systems), with threat mapping to understand how attackers would actually move inside your environment.
Our non-linear defense strategies anticipate real-world adversary behavior, not just generic threats, and provide incident triage and response support to help you contain, investigate, and recover quickly if a serious issue does arise.
Because we’re fintech insiders, we don’t just secure systems in theory — we secure them in the reality of live transactions, crypto flows, and compliance requirements.
Don’t wait for a breach to test your defenses. Schedule a full attack exposure assessment with Clovr Labs and gain clarity on where you stand today.